R
Realcarder
Guest
Step 3Open an Exploit
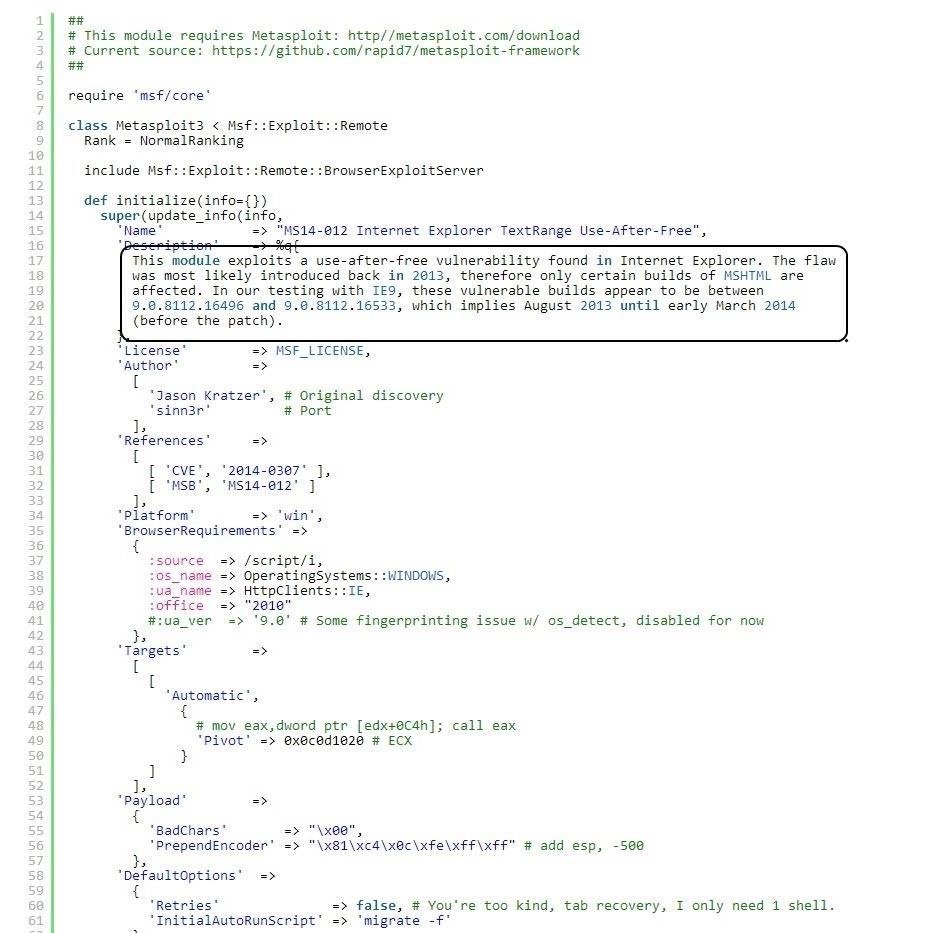
[FONT=&]From the search results page, we can click on any of the two pages of search results and it will take us to the particular exploit. I clicked on the very first exploit in the list "Internet Explorer TextRange Use-After Free (MS14_012)". When I do so, I am brought to a screen that displays the exploit code like that below. I have circled the description in the code of the exploit.[/FONT]
[FONT=&]This exploit works against Internet Explorer that was built between August 2013 and March 2014. If you want to use it, you can simply copy and paste this text file and put it into the exploit directory in Metasploit (if you are using an up-to-date version of Metasploit, it is already included). This is a good example of how specific an exploit can be.[/FONT]Step 4Open Up Searchsploit
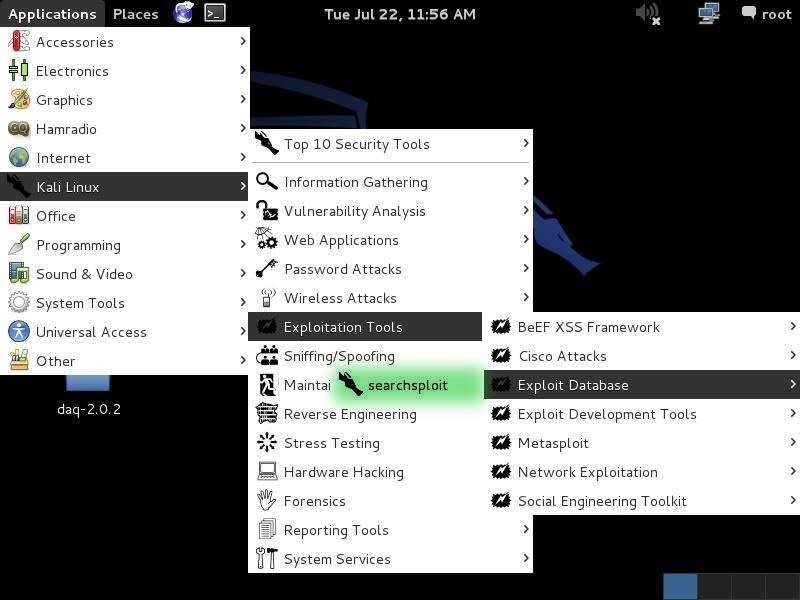
[FONT=&]Kali, having also been developed by Offensive Security, has built into it a local database of exploits based on the same Exploit Database. We can access it by going to Applications -> Kali Linux -> Exploitation Tools -> Exploit Database and clicking on searchsploit as shown below.[/FONT]
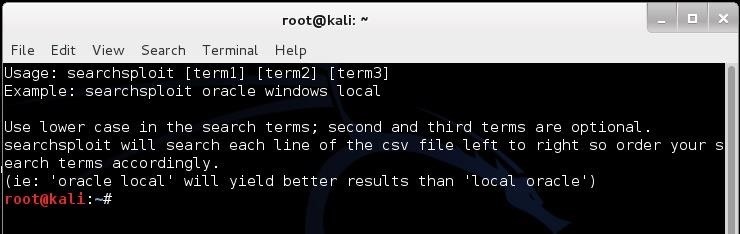
[FONT=&]It will open a screen like that below that details the basic syntax on how to use searchsploit. Note that it explains that you must use lowercase search terms and that it searches a CSV (comma separated values) file from left to right, so search term order matters.[/FONT]
Step 5Search the Exploit Database with Searchsploit
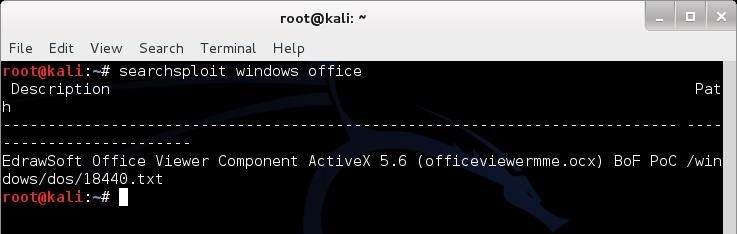
[FONT=&]Now that we have opened a terminal for searchsploit, we can now use this tool to search our local copy of the Exploit Database. As you might expect, our local copy of the exploit database is much faster to search, but does NOT have all the updates that the online database does. Despite this, unless we looking for the very latest exploits, the local database works fast and is effective.[/FONT][FONT=&]One other note on its use. As the information is organized in CSV files, searches locally often will yield results slightly differently than the online database. In the screenshot below, I searched for "Windows" and "Office" and only received a single result, unlike what I received when I used the online database.[/FONT]
[FONT=&]Exploit Database is an excellent repository for exploits and other hacks that we might need, including new Google hacks, white papers on security and hacking, denial of service (DOS) attacks, and shellcode that you can use out the box or tailor for your unique attack.
[/FONT]
[FONT=&]From the search results page, we can click on any of the two pages of search results and it will take us to the particular exploit. I clicked on the very first exploit in the list "Internet Explorer TextRange Use-After Free (MS14_012)". When I do so, I am brought to a screen that displays the exploit code like that below. I have circled the description in the code of the exploit.[/FONT]
[FONT=&]This exploit works against Internet Explorer that was built between August 2013 and March 2014. If you want to use it, you can simply copy and paste this text file and put it into the exploit directory in Metasploit (if you are using an up-to-date version of Metasploit, it is already included). This is a good example of how specific an exploit can be.[/FONT]Step 4Open Up Searchsploit
[FONT=&]Kali, having also been developed by Offensive Security, has built into it a local database of exploits based on the same Exploit Database. We can access it by going to Applications -> Kali Linux -> Exploitation Tools -> Exploit Database and clicking on searchsploit as shown below.[/FONT]
[FONT=&]It will open a screen like that below that details the basic syntax on how to use searchsploit. Note that it explains that you must use lowercase search terms and that it searches a CSV (comma separated values) file from left to right, so search term order matters.[/FONT]
Step 5Search the Exploit Database with Searchsploit
[FONT=&]Now that we have opened a terminal for searchsploit, we can now use this tool to search our local copy of the Exploit Database. As you might expect, our local copy of the exploit database is much faster to search, but does NOT have all the updates that the online database does. Despite this, unless we looking for the very latest exploits, the local database works fast and is effective.[/FONT][FONT=&]One other note on its use. As the information is organized in CSV files, searches locally often will yield results slightly differently than the online database. In the screenshot below, I searched for "Windows" and "Office" and only received a single result, unlike what I received when I used the online database.[/FONT]
[FONT=&]Exploit Database is an excellent repository for exploits and other hacks that we might need, including new Google hacks, white papers on security and hacking, denial of service (DOS) attacks, and shellcode that you can use out the box or tailor for your unique attack.
[/FONT]