- 914
- 246
IBM X-Force researchers have discovered a new malware called Slopoly, which appears to have been created using generative AI. The malware was used in an attack using the Interlock ransomware, allowing the attackers to persist on the compromised system for over a week and steal data.
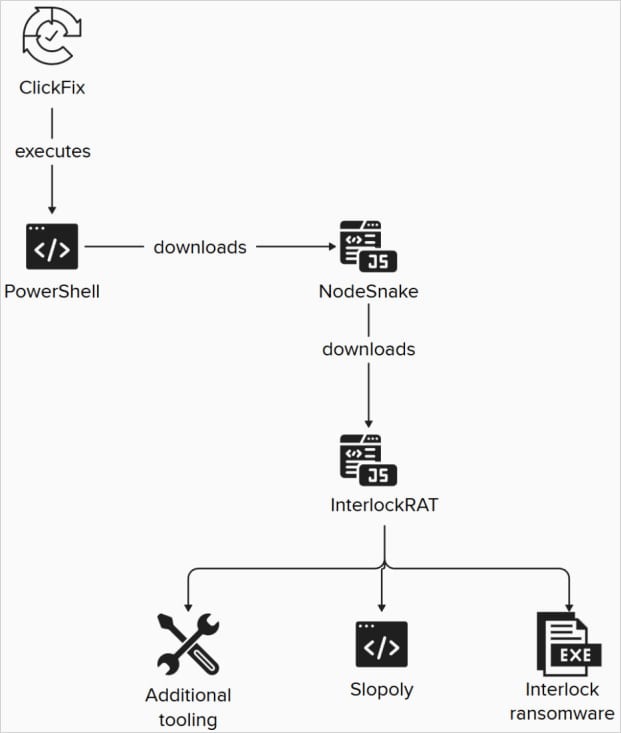
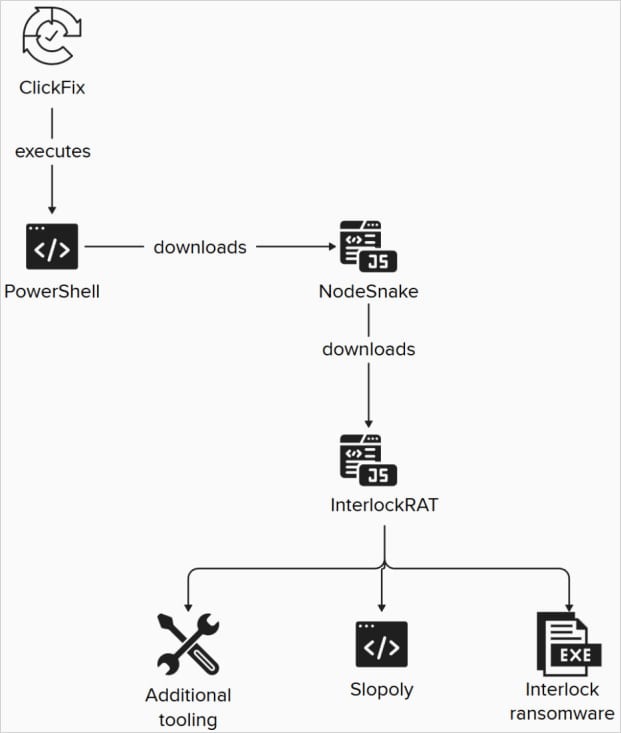
Experts say the attack began with social engineering and the ClickFix technique, and later, the hackers deployed the Slopoly backdoor—a PowerShell script acting as a client for a C2 framework—on the victim's system.
Researchers examined this script and found clear signs of being written by a large-scale language model (LLM): detailed comments in the code, structured logging, proper error handling, and clear variable names. This is highly unusual for human-written malware.
Researchers attribute this attack to the financially motivated group Hive0163, which specializes in extortion, mass data theft, and ransomware.
Analysts note, however, that Slopoly is hardly technically advanced malware. Although the script's comments describe it as a "Polymorphic C2 Persistence Client," researchers found no polymorphic capabilities—the script is unable to modify its code during execution. However, the builder that generates Slopoly can create new instances with randomized configuration values and function names.
The malware hides in C:\ProgramData\Microsoft\Windows\Runtime\ and can collect system information, send heartbeat requests to the command and control server every 30 seconds, poll the server for commands every 50 seconds, execute the received commands via cmd.exe, and send the results back to its operators. The malware persists in the system using a scheduled task named "Runtime Broker."
The malware's supported commands include downloading and running EXE, DLL, and JavaScript payloads, executing shell commands, changing the interval between requests, updating itself, and terminating its own process.
In addition to Slopoly, the detected attack also used the NodeSnake and InterlockRAT backdoors. The Interlock ransomware itself was delivered via the JunkFiction downloader as a 64-bit Windows file, which can be executed as a scheduled task with SYSTEM privileges. The malware uses the Windows Restart Manager API to unlock occupied files and appends the .!NT3RLOCK or .int3R1Ock extensions to encrypted files.
The Interlock group emerged in 2024 and was one of the first to use ClickFix -type attacks , as well as their FileFix variant.According to researchers, Hive0163 may be linked to the developers of Broomstick, SocksShell, PortStarter, and SystemBC malware, as well as the operators of the Rhysida ransomware.
Experts say the attack began with social engineering and the ClickFix technique, and later, the hackers deployed the Slopoly backdoor—a PowerShell script acting as a client for a C2 framework—on the victim's system.
Researchers examined this script and found clear signs of being written by a large-scale language model (LLM): detailed comments in the code, structured logging, proper error handling, and clear variable names. This is highly unusual for human-written malware.
Researchers attribute this attack to the financially motivated group Hive0163, which specializes in extortion, mass data theft, and ransomware.
Analysts note, however, that Slopoly is hardly technically advanced malware. Although the script's comments describe it as a "Polymorphic C2 Persistence Client," researchers found no polymorphic capabilities—the script is unable to modify its code during execution. However, the builder that generates Slopoly can create new instances with randomized configuration values and function names.
The malware hides in C:\ProgramData\Microsoft\Windows\Runtime\ and can collect system information, send heartbeat requests to the command and control server every 30 seconds, poll the server for commands every 50 seconds, execute the received commands via cmd.exe, and send the results back to its operators. The malware persists in the system using a scheduled task named "Runtime Broker."
The malware's supported commands include downloading and running EXE, DLL, and JavaScript payloads, executing shell commands, changing the interval between requests, updating itself, and terminating its own process.
In addition to Slopoly, the detected attack also used the NodeSnake and InterlockRAT backdoors. The Interlock ransomware itself was delivered via the JunkFiction downloader as a 64-bit Windows file, which can be executed as a scheduled task with SYSTEM privileges. The malware uses the Windows Restart Manager API to unlock occupied files and appends the .!NT3RLOCK or .int3R1Ock extensions to encrypted files.
The Interlock group emerged in 2024 and was one of the first to use ClickFix -type attacks , as well as their FileFix variant.According to researchers, Hive0163 may be linked to the developers of Broomstick, SocksShell, PortStarter, and SystemBC malware, as well as the operators of the Rhysida ransomware.
