Doctor Web experts have warned about the spread of the JobStealer Trojan, which attacks macOS and Windows users. The malware primarily targets cryptocurrency wallets, but also collects passwords, cookies, browser data, Telegram accounts, and other confidential information.
The scheme begins as a typical job offer. Attackers contact potential victims, offer the vacancy, and invite them to an online interview. To do this, they send a link to a website supposedly featuring a video conferencing platform.
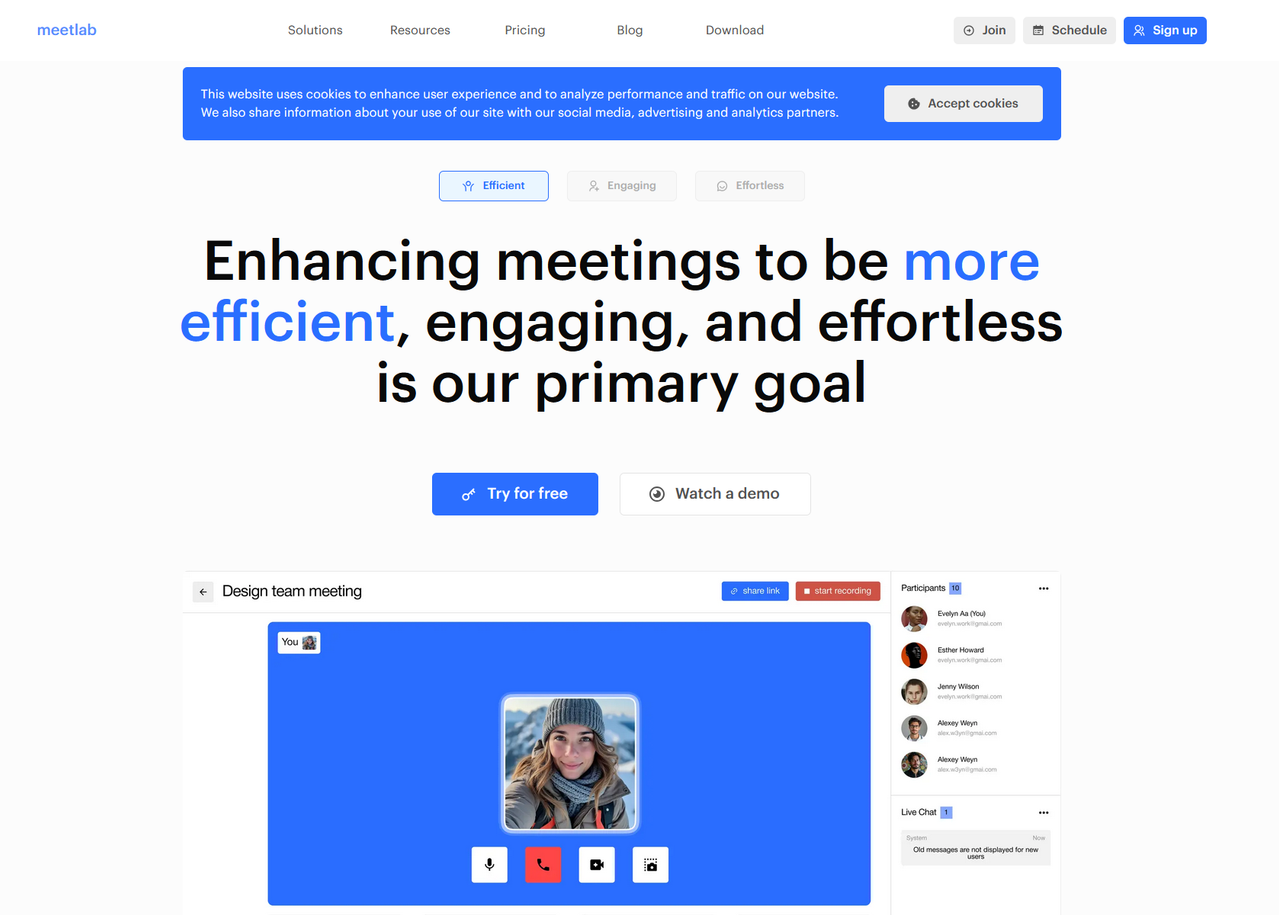
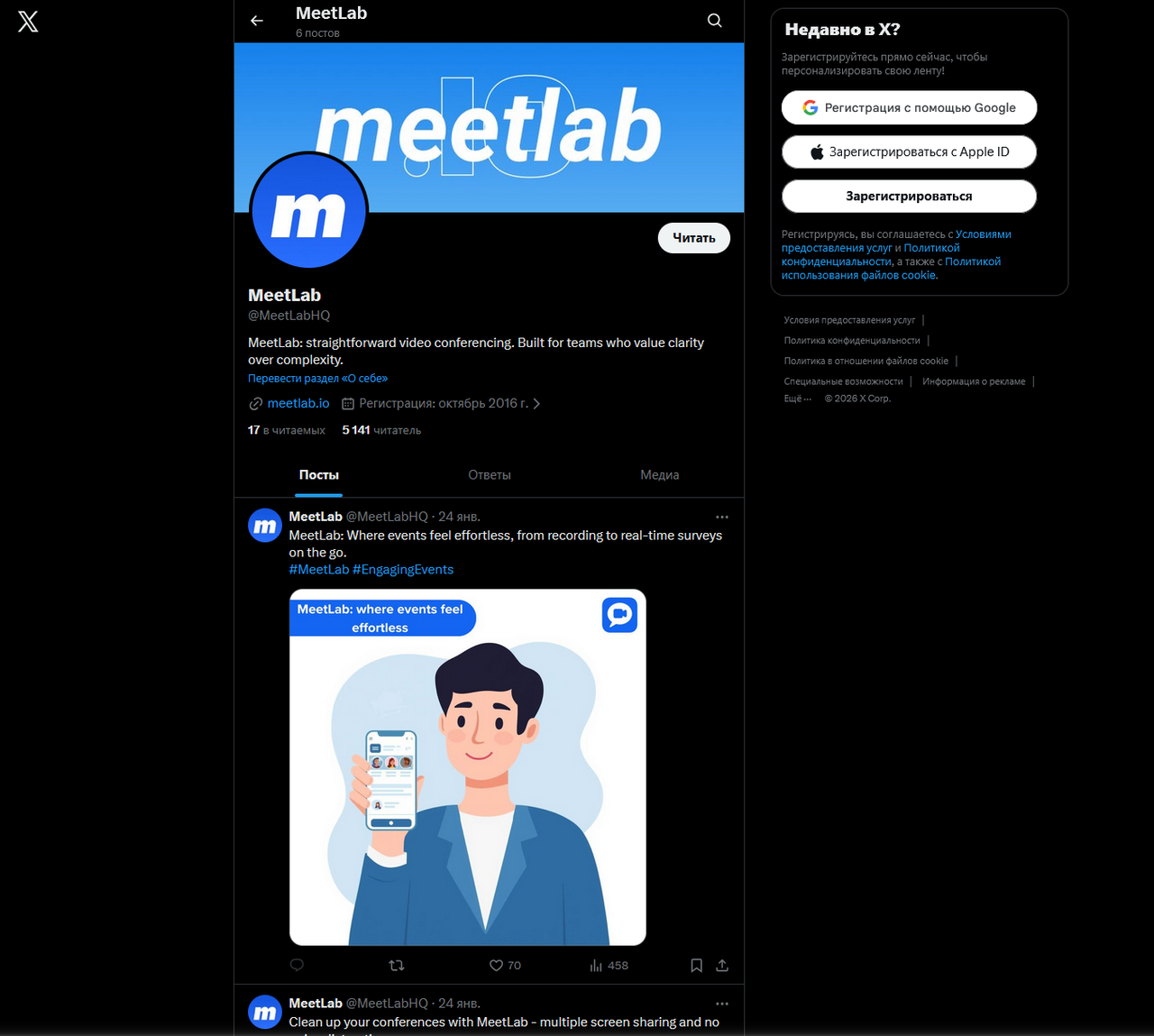
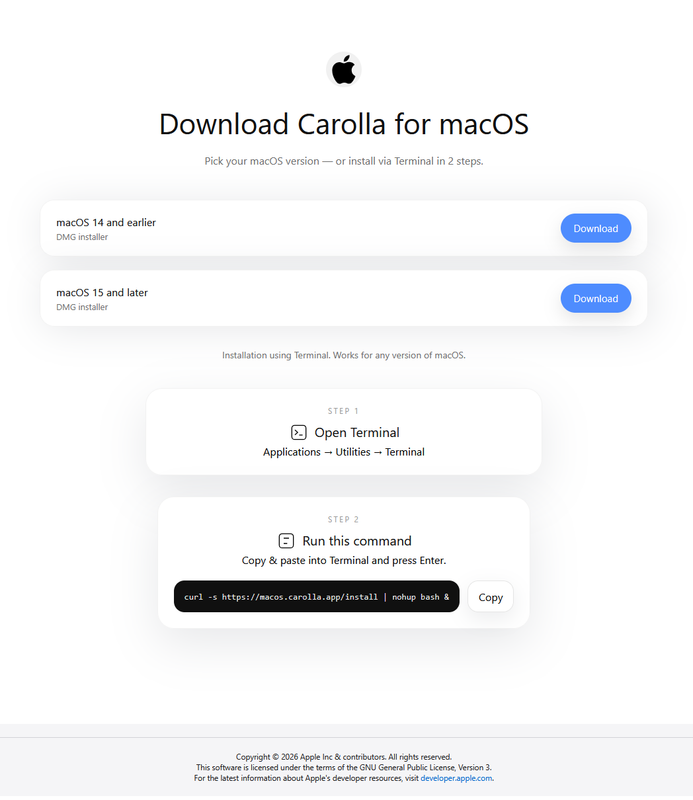
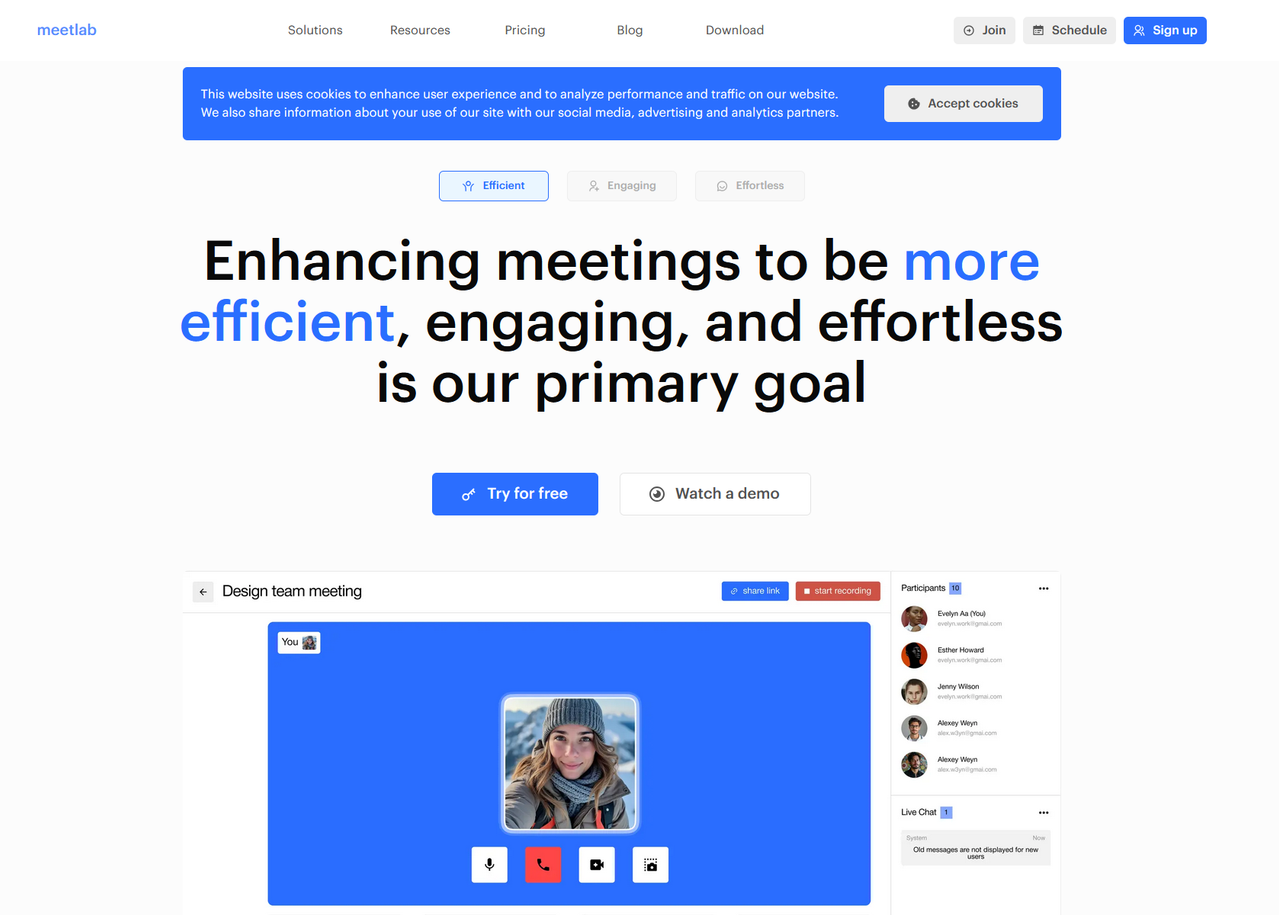
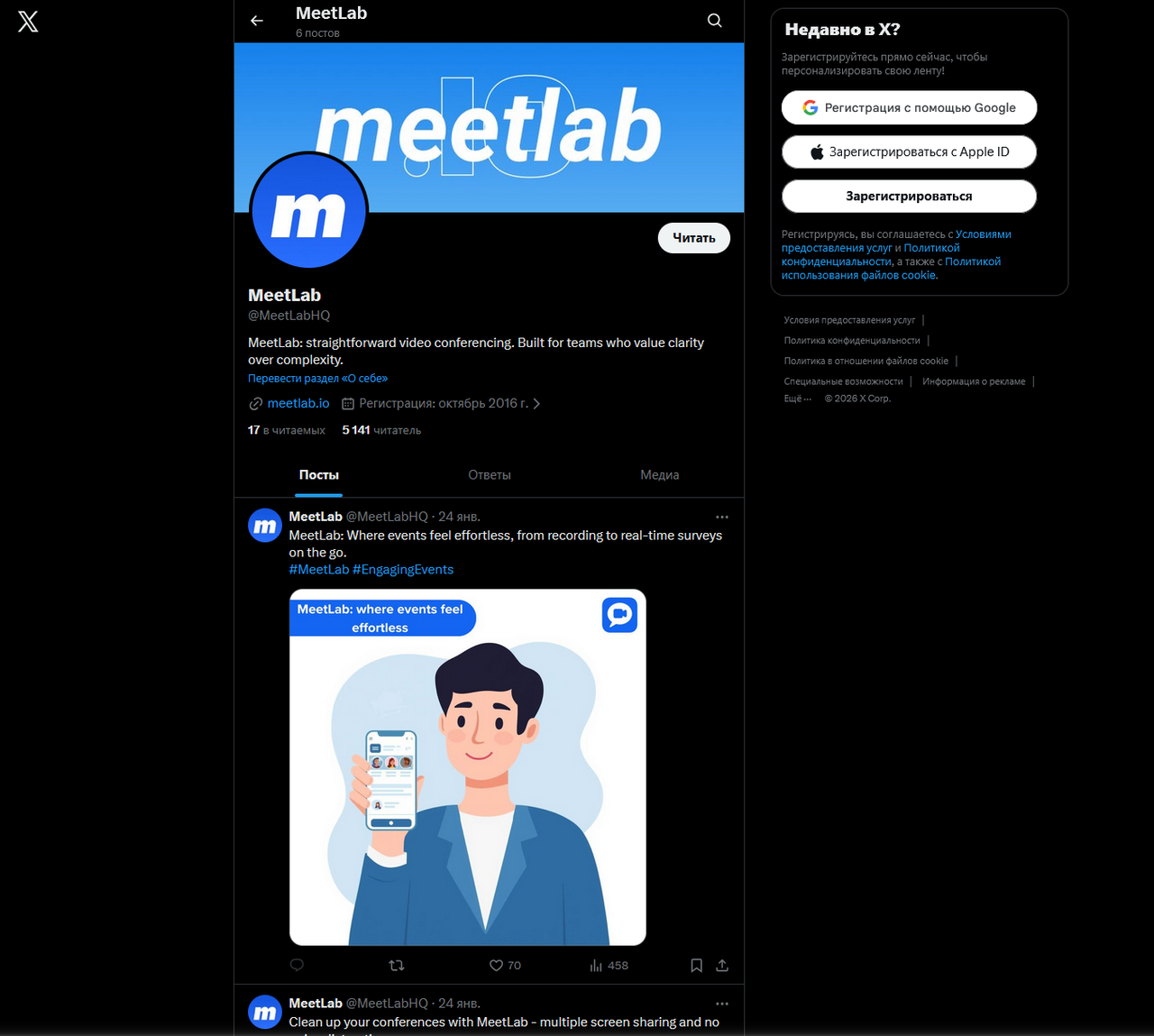
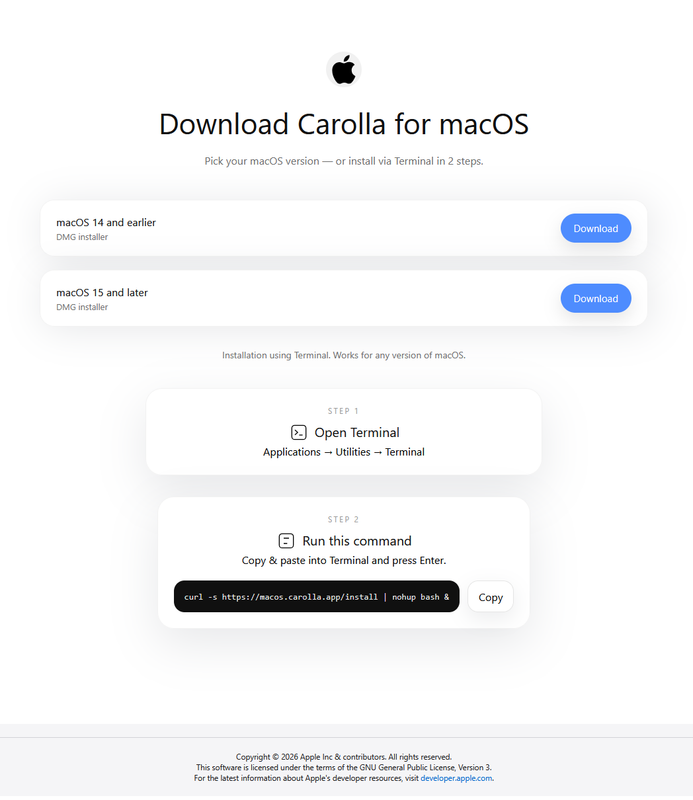
The websites appear quite neat and imitate legitimate services. Scammers use various names: MeetLab, Juseo, Meetix, Carolla, and others. In some cases, they even disguise themselves as well-known solutions like Webex. To make the attack more convincing, they create Telegram channels and social media accounts to give the service a semblance of real life. On macOS, victims are offered two installation options: download the .dmg image or copy the command and execute it in the terminal. In both cases, JobStealer launches instead of the video interview app. Once launched, the Trojan displays a phishing window with an error message and asks to enter the user's macOS account password, supposedly to fix the problem. It then begins collecting data: system information, cookies, saved passwords, bank cards from autofill, data from hundreds of browser add-ons, Telegram files, notes from the Notes app, and information about Ledger Live and Trezor Suite. The collected data is packaged into a ZIP archive and sent to the attackers' command-and-control server. The Windows version of JobStealer operates similarly. Some fraudulent websites also have sections for Linux, iOS, and Android, but analysts have not yet recorded any actual distribution of these variants. However, it cannot be ruled out that the attackers will add them later.
The scheme begins as a typical job offer. Attackers contact potential victims, offer the vacancy, and invite them to an online interview. To do this, they send a link to a website supposedly featuring a video conferencing platform.
The websites appear quite neat and imitate legitimate services. Scammers use various names: MeetLab, Juseo, Meetix, Carolla, and others. In some cases, they even disguise themselves as well-known solutions like Webex. To make the attack more convincing, they create Telegram channels and social media accounts to give the service a semblance of real life. On macOS, victims are offered two installation options: download the .dmg image or copy the command and execute it in the terminal. In both cases, JobStealer launches instead of the video interview app. Once launched, the Trojan displays a phishing window with an error message and asks to enter the user's macOS account password, supposedly to fix the problem. It then begins collecting data: system information, cookies, saved passwords, bank cards from autofill, data from hundreds of browser add-ons, Telegram files, notes from the Notes app, and information about Ledger Live and Trezor Suite. The collected data is packaged into a ZIP archive and sent to the attackers' command-and-control server. The Windows version of JobStealer operates similarly. Some fraudulent websites also have sections for Linux, iOS, and Android, but analysts have not yet recorded any actual distribution of these variants. However, it cannot be ruled out that the attackers will add them later.