- 922
- 247
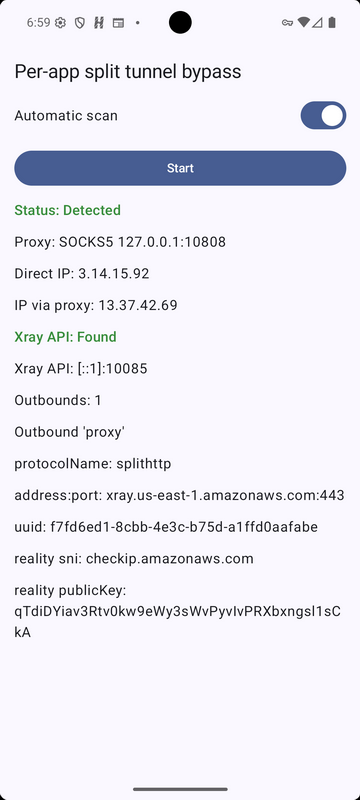
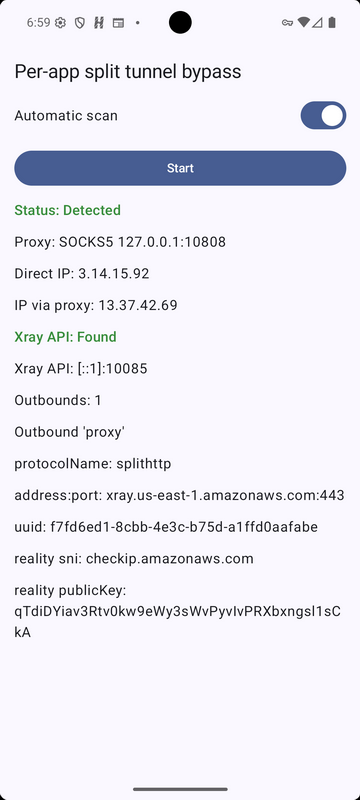
A user named runetfreedom reported on Habr about a serious issue affecting most mobile VLESS clients based on xray and sing-box. The bug allows one to determine the proxy server's actual outgoing IP and bypass per-app split tunneling, and in the case of one client, extract user configuration files.
According to the specialist, the root of the problem lies in the architecture itself: clients set up a local Socks5 proxy on the device without authorization. Split tunneling by apps is implemented through the system VpnService, which routes traffic to tun2socks, then to Socks5 and then to the VPN server. If a spy module is present on the device (for example, as part of an app), nothing prevents it from directly accessing this Socks5 proxy, bypassing VpnService, and discovering the outgoing IP.
According to the researcher, isolating via private spaces in Android (Knox, Shelter, Island, and other similar clients) won't help either: VpnService is indeed isolated in these environments, but the loopback interface is not. This means that potential malware can scan localhost and detect open Socks5 even from a private environment. This is particularly dangerous, as it creates a false sense of security for the user.
The author of the publication posted a proof-of-concept for bypassing split tunneling on GitHub .
On March 10, 2026, the researcher sent information about the issue to the developers of all popular clients. However, as of April 7, 2026, when the publication was published on Habr, no one had patched the vulnerability.
Runetfreedom lists the following vulnerable clients: v2RayTun, V2BOX, v2rayNG, Hiddify, Exclave, Npv Tunnel, Neko Box, as well as most typical Clash and Sing-box configurations.
The article specifically focuses on the Happ client. According to the researcher, it launches the xray API with the HandlerService enabled without any authorization, allowing for the extraction of user configurations along with keys, the server's input IP, and SNI. If this is coupled with another common xray configuration error (the researcher does not disclose the details), it would theoretically even be possible to decrypt traffic. It is also emphasized that the client was recently removed from the Russian App Store, so its team will no longer be able to technically release an update.
Happ's developers attributed the active HandlerService to "collecting connection statistics," but the author of the study dismissed this as an excuse, noting that LogService would have been sufficient.
The researcher also draws attention to a recent manual that representatives of the Ministry of Digital Development, according to media reports, recently sent out .Large Russian companies. He notes that the document lists typical ports for SOCKS, HTTP, and transparent proxies, as well as Tor. Therefore, runetfreedom believes that the regulator is either already aware of the bug or is about to discover it independently. In the article, the author lists a number of possible technical measures to mitigate the risks.
After runetfreedom's publication, Happ developers initially denied acknowledging the discovery as a vulnerability, but then, under community pressure, promised to fix both issues.
According to the specialist, the root of the problem lies in the architecture itself: clients set up a local Socks5 proxy on the device without authorization. Split tunneling by apps is implemented through the system VpnService, which routes traffic to tun2socks, then to Socks5 and then to the VPN server. If a spy module is present on the device (for example, as part of an app), nothing prevents it from directly accessing this Socks5 proxy, bypassing VpnService, and discovering the outgoing IP.
According to the researcher, isolating via private spaces in Android (Knox, Shelter, Island, and other similar clients) won't help either: VpnService is indeed isolated in these environments, but the loopback interface is not. This means that potential malware can scan localhost and detect open Socks5 even from a private environment. This is particularly dangerous, as it creates a false sense of security for the user.
The author of the publication posted a proof-of-concept for bypassing split tunneling on GitHub .
On March 10, 2026, the researcher sent information about the issue to the developers of all popular clients. However, as of April 7, 2026, when the publication was published on Habr, no one had patched the vulnerability.
Runetfreedom lists the following vulnerable clients: v2RayTun, V2BOX, v2rayNG, Hiddify, Exclave, Npv Tunnel, Neko Box, as well as most typical Clash and Sing-box configurations.
The article specifically focuses on the Happ client. According to the researcher, it launches the xray API with the HandlerService enabled without any authorization, allowing for the extraction of user configurations along with keys, the server's input IP, and SNI. If this is coupled with another common xray configuration error (the researcher does not disclose the details), it would theoretically even be possible to decrypt traffic. It is also emphasized that the client was recently removed from the Russian App Store, so its team will no longer be able to technically release an update.
Happ's developers attributed the active HandlerService to "collecting connection statistics," but the author of the study dismissed this as an excuse, noting that LogService would have been sufficient.
The researcher also draws attention to a recent manual that representatives of the Ministry of Digital Development, according to media reports, recently sent out .Large Russian companies. He notes that the document lists typical ports for SOCKS, HTTP, and transparent proxies, as well as Tor. Therefore, runetfreedom believes that the regulator is either already aware of the bug or is about to discover it independently. In the article, the author lists a number of possible technical measures to mitigate the risks.
After runetfreedom's publication, Happ developers initially denied acknowledging the discovery as a vulnerability, but then, under community pressure, promised to fix both issues.
