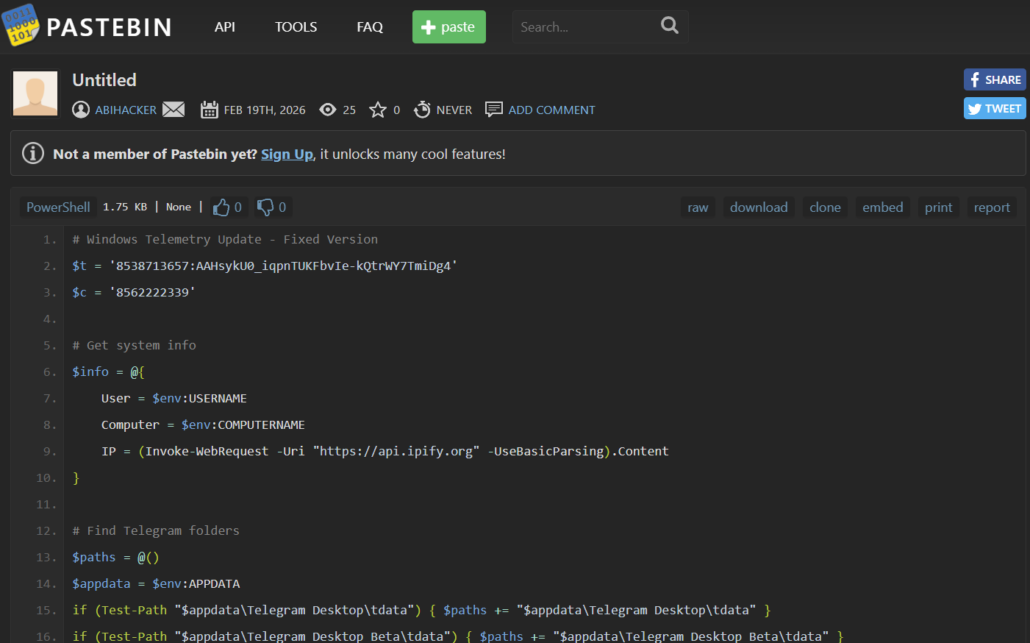
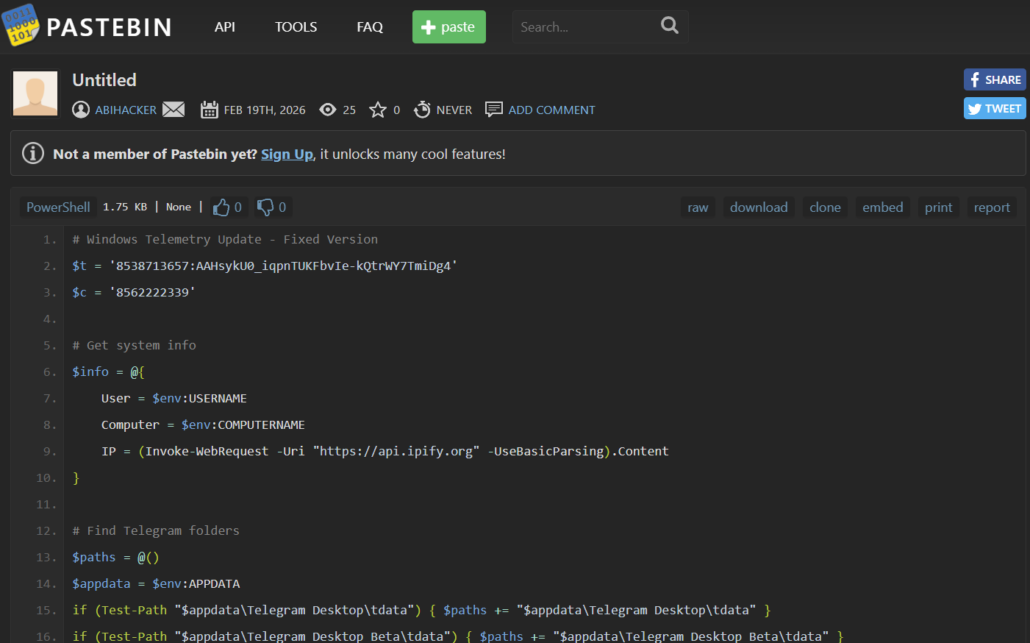
Researchers have discovered a new experimental stealer that targets desktop Telegram sessions rather than passwords and browser cookies. The tool was hidden in a PowerShell script on Pastebin, disguised as a patched Windows update.
The malware is clearly still in testing, so analysts were able to analyze a draft containing public Telegram bot tokens, a chat ID, and debugging traces.
The script uses hardcoded Telegram bot credentials and sends the stolen data via the Telegram Bot API. The bot was named afhbhfsdvfh_bot , and its description listed "Telegram attacker"—a rather subtle approach to disguise.
Once launched, the script collects basic system information: username, hostname, and public IP address via api.ipify[.]org . It adds this data to the archive signature, so the operator can immediately identify the source of the loot.
The main target is the tdata folders in Telegram Desktop and Telegram Desktop Beta's AppData. This is where MTProto's long-lived authentication keys are stored. If an attacker gains access to these, they can hijack a Telegram session without a password or SMS code.
If such folders are found, the script terminates the Telegram.exe process to unlock the files, packs the found data into a diag.zip archive in a temporary directory, and sends it via the sendDocument method of the Telegram Bot API. If the primary delivery method fails, a fallback option via WebClient is provided : the signature with metadata may be lost, but the archive itself will still be sent to the attacker. Researchers found two versions of the script. The first contained an error in the download mechanism, while the second correctly generated the request and added basic error handling. Furthermore, if Telegram is not found on the machine, the second version still sends a notification to the operator, effectively turning each launch into a check for target availability. There are no signs of widespread distribution yet. The script is not obfuscated, does not contain a persistence mechanism, and does not have a full-fledged delivery system. Furthermore, telemetry for the exposed token did not show any actual transmissions of diag.zip archives during the observation period. This all looks more like lab tests than an active campaign. @ Anti-Malware
The malware is clearly still in testing, so analysts were able to analyze a draft containing public Telegram bot tokens, a chat ID, and debugging traces.
The script uses hardcoded Telegram bot credentials and sends the stolen data via the Telegram Bot API. The bot was named afhbhfsdvfh_bot , and its description listed "Telegram attacker"—a rather subtle approach to disguise.
Once launched, the script collects basic system information: username, hostname, and public IP address via api.ipify[.]org . It adds this data to the archive signature, so the operator can immediately identify the source of the loot.
The main target is the tdata folders in Telegram Desktop and Telegram Desktop Beta's AppData. This is where MTProto's long-lived authentication keys are stored. If an attacker gains access to these, they can hijack a Telegram session without a password or SMS code.
If such folders are found, the script terminates the Telegram.exe process to unlock the files, packs the found data into a diag.zip archive in a temporary directory, and sends it via the sendDocument method of the Telegram Bot API. If the primary delivery method fails, a fallback option via WebClient is provided : the signature with metadata may be lost, but the archive itself will still be sent to the attacker. Researchers found two versions of the script. The first contained an error in the download mechanism, while the second correctly generated the request and added basic error handling. Furthermore, if Telegram is not found on the machine, the second version still sends a notification to the operator, effectively turning each launch into a check for target availability. There are no signs of widespread distribution yet. The script is not obfuscated, does not contain a persistence mechanism, and does not have a full-fledged delivery system. Furthermore, telemetry for the exposed token did not show any actual transmissions of diag.zip archives during the observation period. This all looks more like lab tests than an active campaign. @ Anti-Malware