- 3,010
- 281
- 1,730
Sucuri analysts have discovered that hackers are using the MU-plugins (Must-Use Plugins) directory in WordPress to hide malicious code and run it without being detected.
The technique was first spotted in February 2025, but the pace of its implementation is growing, and attackers are currently abusing MU-plugins to run three different types of malicious code.
Must-Use Plugins are a special type of WordPress plugin that run on every page load and do not require activation in the admin panel. They are PHP files stored in the wp-content/mu-plugins/ directory that are automatically executed on page load and do not appear in the admin panel on the Plugins page unless the Must-Use filter is selected.
Such plugins are used, for example, to force custom security rules to work site-wide, improve performance, dynamically modify variables, and so on.
Since MU plugins run on every page load and do not appear in the standard plugin list, they can be used to covertly perform a wide range of malicious actions, including stealing credentials, injecting malicious code, or modifying HTML output.
Sucuri researchers have discovered three payloads that attackers place in the MU plugins directory:
The researchers believe that the most dangerous of these samples is the web shell, as it allows attackers to remotely execute commands on the server, steal data, and carry out subsequent attacks on users and visitors of the resource.
The other two malware are more likely to damage the reputation of the site and its SEO indicators due to suspicious redirects and attempts to install malware on visitors' computers.
So far, Sucuri researchers have not been able to establish the exact method of infecting the affected sites. It is assumed that the attackers exploit already known vulnerabilities in plugins and themes for WordPress or weak administrator credentials.
The technique was first spotted in February 2025, but the pace of its implementation is growing, and attackers are currently abusing MU-plugins to run three different types of malicious code.
Must-Use Plugins are a special type of WordPress plugin that run on every page load and do not require activation in the admin panel. They are PHP files stored in the wp-content/mu-plugins/ directory that are automatically executed on page load and do not appear in the admin panel on the Plugins page unless the Must-Use filter is selected.
Such plugins are used, for example, to force custom security rules to work site-wide, improve performance, dynamically modify variables, and so on.
Since MU plugins run on every page load and do not appear in the standard plugin list, they can be used to covertly perform a wide range of malicious actions, including stealing credentials, injecting malicious code, or modifying HTML output.
Sucuri researchers have discovered three payloads that attackers place in the MU plugins directory:
- redirect.php : Redirects visitors (excluding bots and logged in administrators) to a malicious site (updatesnow[.]net) that displays a fake browser update prompt to trick the victim into downloading malware;
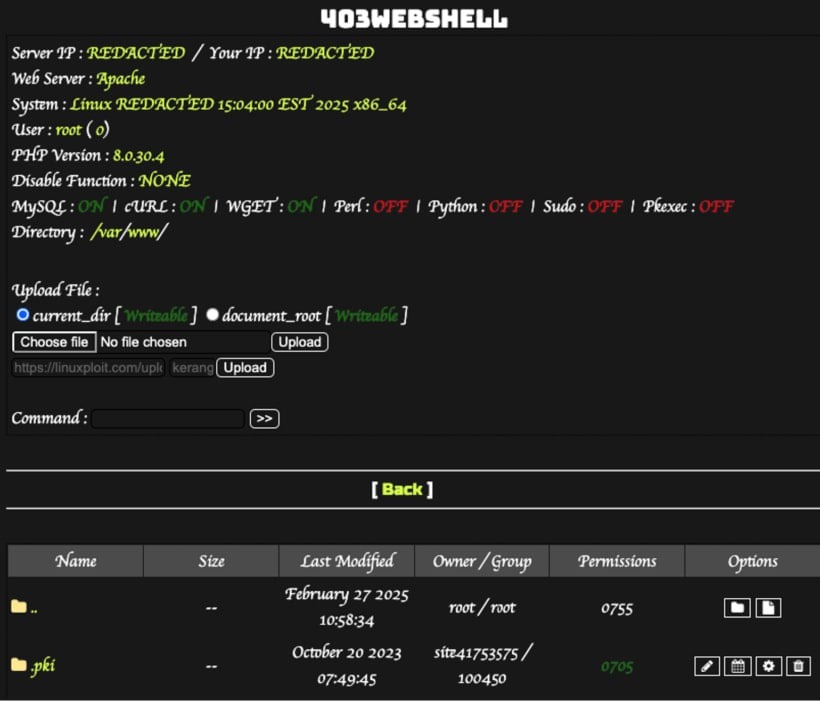
- index.php : a web shell that acts as a backdoor, fetching and executing PHP code from a GitHub repository;
- custom-js-loader.php : Loads JavaScript that replaces all images on the site with explicit content and intercepts all external links, opening fraudulent pop-ups instead.
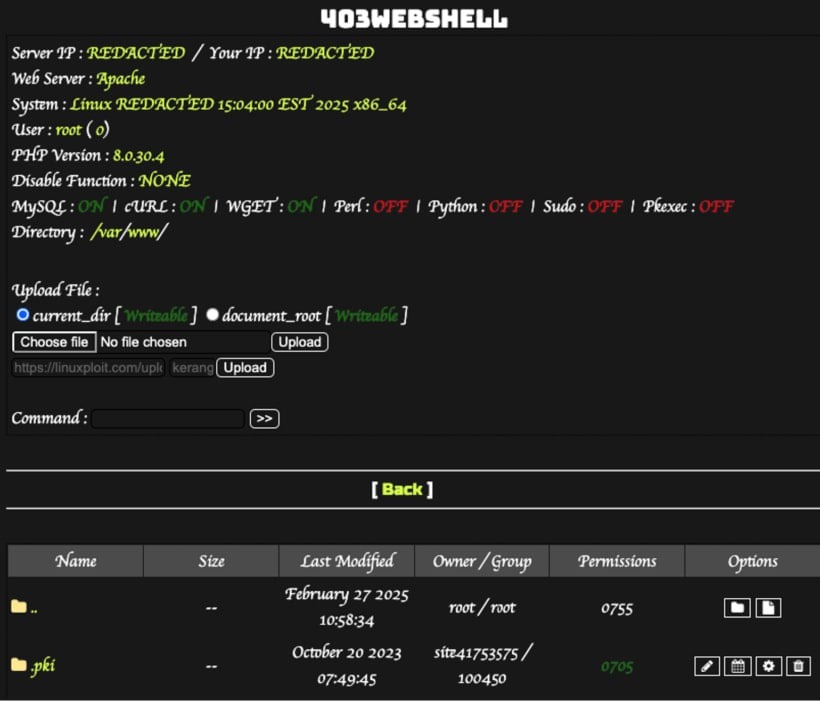
The researchers believe that the most dangerous of these samples is the web shell, as it allows attackers to remotely execute commands on the server, steal data, and carry out subsequent attacks on users and visitors of the resource.
The other two malware are more likely to damage the reputation of the site and its SEO indicators due to suspicious redirects and attempts to install malware on visitors' computers.
So far, Sucuri researchers have not been able to establish the exact method of infecting the affected sites. It is assumed that the attackers exploit already known vulnerabilities in plugins and themes for WordPress or weak administrator credentials.
