- 921
- 246
Drift Protocol lost $285 million in a North Korean hacker attack that was planned for over six months. The UNC4736 group carried out a large-scale social engineering operation, building trust with project contributors beginning in the fall of 2025.
Drift Protocol is a DeFi platform built on the Solana blockchain, operating as a non-custodial exchange where traders retain full control of their funds. By the end of 2024, the platform had 200,000 traders, and its total trading volume exceeded $55 billion.
According to Drift , preparations for the attack began as early as March 11. Then, the attackers withdrew 10 ETH from Tornado Cash and used these funds to create a completely fictitious token, CarbonVote Token (CVT), with 750 million units. On the decentralized exchange Raydium, hackers created a liquidity pool with just $500 and, over the course of several weeks, inflated volumes using wash trading (fake trades with themselves), artificially maintaining the price of CVT around $1. Drift's price oracles accepted this trading history as real and began treating CVT as a legitimate asset.
Simultaneously, from March 23 to 30, the attackers created durable nonce accounts. Durable nonces are a legitimate Solana mechanism that allows transactions to be signed in advance and executed later, bypassing the standard expiration window (usually 60-90 seconds).
Using social engineering, the hackers convinced two of the five Security Council members to sign transactions that appeared routine—this was enough to overcome the multisig threshold.
A critical factor was also the fact that on March 27, Drift conducted a scheduled Security Council migration and removed the timelock—an administrative delay that typically gives the community 24-72 hours to detect suspicious activity. On
April 1, all of the above came together. First, a test withdrawal was performed, and a minute later, the attackers launched pre-signed durable nonce transactions and seized administrative control.
Having gained privileges, they added CVT as an acceptable collateral asset to Drift, raised withdrawal limits to enormous amounts (500 trillion—effectively disabling protection), and deposited hundreds of millions of CVT tokens as collateral. Based on the price fabricated by oracles, this collateral appeared valuable, and the hackers withdrew real assets, including USDC, JLP, and other tokens, using 31 transactions in just 12 minutes.
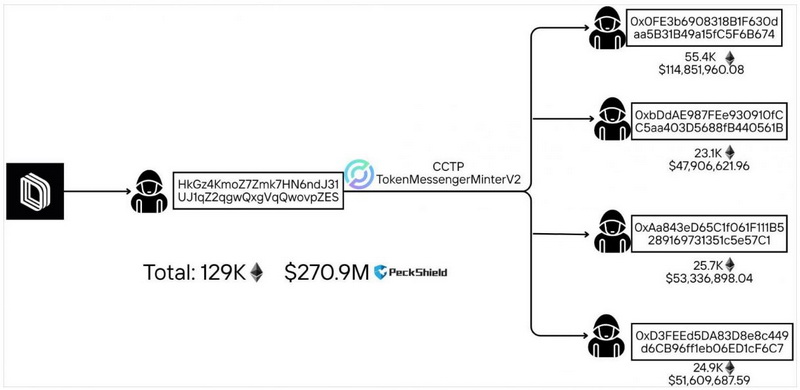
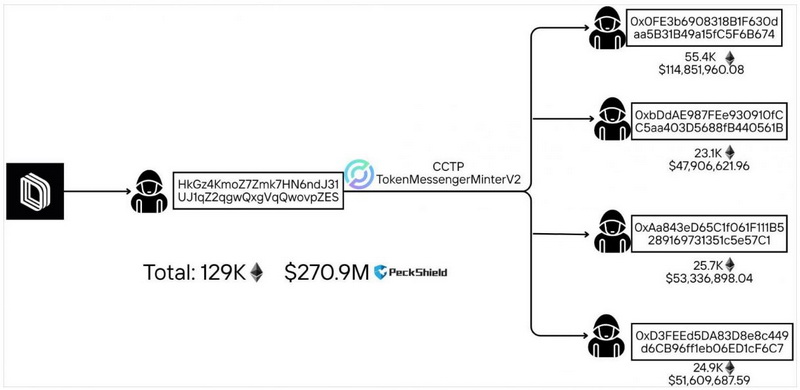
Drift estimates the total losses to be around $280 million, although blockchain analysts at PeckShield estimate the damage to be $285 million.
Drift emphasizes that no vulnerabilities were found in smart contracts or the platform's software code, and seed phrases were not compromised.
Researchers at Elliptic and TRM Labs soon linked the attack to North Korean hackers based on on-chain indicators: the use of Tornado Cash, cross-chain bridging patterns, and rapid money laundering, all characteristic of North Korean groups.
Experts place responsibility for the incident, with moderate certainty, on UNC4736 (aka AppleJeus, Citrine Sleet, Golden Chollima, and Gleaming Pisces). This hacking group has been targeting the cryptocurrency sector since at least 2018 and is best known for its 2023 attack on the 3CX supply chain and the $53 million hack of the DeFi platform Radiant Capital in October 2024. Details
of social engineering attacks carried out by hackers since the fall of 2025 have also been revealed . Posing as employees of a trading company, the attackers contacted Drift contributors at major crypto conferences. They were technically savvy, had verifiable professional backgrounds, and were well versed in Drift's design. After this introduction, the conversations continued on Telegram—months of detailed discussions about trading strategies and integration with the protocol.
Between December 2025 and January 2026, the group deployed its own Ecosystem Vault on Drift, filled out a strategy form, and contributed over $1 million of its own funds. This was done to build trust and establish a foothold within the ecosystem. The front men continued to communicate with contributors right up until the attack.
The investigation ultimately revealed two potential compromise vectors. One contributor may have been compromised after cloning a code repository provided by the attackers. The malicious Visual Studio Code project used a tasks.json file with the runOn:folderOpen option, automatically running the malicious code when the project was opened in the IDE.
The second contributor installed a wallet through Apple TestFlight, ostensibly for beta testing.
The attack affected borrow/lend deposits, vault funds, and trading funds. All protocol functions are currently frozen, although Drift notes that DSOL is unaffected and the insurance fund is secure.
The developers are collaborating with security experts, cryptocurrency exchanges, and law enforcement agencies to track down and freeze the stolen funds. A more detailed report on the incident will be published in the coming days.
Drift Protocol is a DeFi platform built on the Solana blockchain, operating as a non-custodial exchange where traders retain full control of their funds. By the end of 2024, the platform had 200,000 traders, and its total trading volume exceeded $55 billion.
According to Drift , preparations for the attack began as early as March 11. Then, the attackers withdrew 10 ETH from Tornado Cash and used these funds to create a completely fictitious token, CarbonVote Token (CVT), with 750 million units. On the decentralized exchange Raydium, hackers created a liquidity pool with just $500 and, over the course of several weeks, inflated volumes using wash trading (fake trades with themselves), artificially maintaining the price of CVT around $1. Drift's price oracles accepted this trading history as real and began treating CVT as a legitimate asset.
Simultaneously, from March 23 to 30, the attackers created durable nonce accounts. Durable nonces are a legitimate Solana mechanism that allows transactions to be signed in advance and executed later, bypassing the standard expiration window (usually 60-90 seconds).
Using social engineering, the hackers convinced two of the five Security Council members to sign transactions that appeared routine—this was enough to overcome the multisig threshold.
A critical factor was also the fact that on March 27, Drift conducted a scheduled Security Council migration and removed the timelock—an administrative delay that typically gives the community 24-72 hours to detect suspicious activity. On
April 1, all of the above came together. First, a test withdrawal was performed, and a minute later, the attackers launched pre-signed durable nonce transactions and seized administrative control.
Having gained privileges, they added CVT as an acceptable collateral asset to Drift, raised withdrawal limits to enormous amounts (500 trillion—effectively disabling protection), and deposited hundreds of millions of CVT tokens as collateral. Based on the price fabricated by oracles, this collateral appeared valuable, and the hackers withdrew real assets, including USDC, JLP, and other tokens, using 31 transactions in just 12 minutes.
Drift estimates the total losses to be around $280 million, although blockchain analysts at PeckShield estimate the damage to be $285 million.
Drift emphasizes that no vulnerabilities were found in smart contracts or the platform's software code, and seed phrases were not compromised.
Researchers at Elliptic and TRM Labs soon linked the attack to North Korean hackers based on on-chain indicators: the use of Tornado Cash, cross-chain bridging patterns, and rapid money laundering, all characteristic of North Korean groups.
Experts place responsibility for the incident, with moderate certainty, on UNC4736 (aka AppleJeus, Citrine Sleet, Golden Chollima, and Gleaming Pisces). This hacking group has been targeting the cryptocurrency sector since at least 2018 and is best known for its 2023 attack on the 3CX supply chain and the $53 million hack of the DeFi platform Radiant Capital in October 2024. Details
of social engineering attacks carried out by hackers since the fall of 2025 have also been revealed . Posing as employees of a trading company, the attackers contacted Drift contributors at major crypto conferences. They were technically savvy, had verifiable professional backgrounds, and were well versed in Drift's design. After this introduction, the conversations continued on Telegram—months of detailed discussions about trading strategies and integration with the protocol.
| "The people who met with our contributors in person were not North Korean citizens," Drift explained. "But North Korean hackers operating at this level are known to use third-party intermediaries to build personal relationships with their victims." |
The investigation ultimately revealed two potential compromise vectors. One contributor may have been compromised after cloning a code repository provided by the attackers. The malicious Visual Studio Code project used a tasks.json file with the runOn:folderOpen option, automatically running the malicious code when the project was opened in the IDE.
The second contributor installed a wallet through Apple TestFlight, ostensibly for beta testing.
The attack affected borrow/lend deposits, vault funds, and trading funds. All protocol functions are currently frozen, although Drift notes that DSOL is unaffected and the insurance fund is secure.
The developers are collaborating with security experts, cryptocurrency exchanges, and law enforcement agencies to track down and freeze the stolen funds. A more detailed report on the incident will be published in the coming days.
