- 926
- 247
Sansec researchers have detected a large-scale payment data theft campaign: malware hides within a single-pixel SVG image and intercepts credit card data during checkout.
Researchers warn that the attack has affected nearly 100 online stores on the Magento platform. The attackers found a sophisticated way to hide the web skimmer: the malware is embedded in the page's HTML code as a 1x1 pixel SVG element with an "onload" handler. The compromise is visually invisible, and scanners don't detect it, but the malicious code is still active. The
"onload" attribute hides the skimmer's entire payload, encoded in base64 via an atob() call and triggered via setTimeout. The experts explain that the attackers don't use external scripts or suspicious links that could alert monitoring systems. The malware is embedded entirely within the page's markup in a single string.
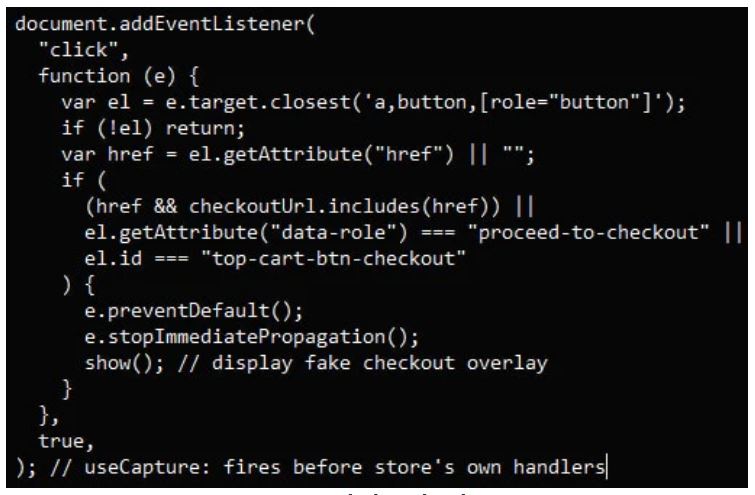
When a customer clicks the "Checkout" button in an infected store, the script intercepts the click and displays a fake "Secure Checkout" window over the page, complete with fields for entering the card number and billing address. This data is validated using the Luhn algorithm in real time and then sent to the attackers: the payload is first XOR-encoded, then base64-encoded, and transmitted to the hackers' server in JSON format.
Researchers identified six data exfiltration domains, all hosted by IncogNet LLC (AS40663) in the Netherlands. Each domain received data from 10-15 confirmed victims.
According to the researchers, the entry point was most likely the recent PolyShell RCE vulnerability , which became known in mid-March. The bug affects all stable installations of Magento Open Source and Adobe Commerce version 2 and allows for arbitrary code execution without authentication, as well as account takeover.
Sansec previously warned that more than half of all vulnerable stores were subject to PolyShell attacks (some of which were ultimately infected with skimmers for data exfiltration via WebRTC).
It's worth noting that Adobe developers have not yet released a patch for production versions of Magento. Currently, the fix is only available in the pre-release 2.4.9-alpha3+, and the company is not commenting on the vulnerability or its exploitation.
Until the official patch is released, experts recommend implementing all available security measures and, if possible, updating to the latest beta version of Magento.
Researchers warn that the attack has affected nearly 100 online stores on the Magento platform. The attackers found a sophisticated way to hide the web skimmer: the malware is embedded in the page's HTML code as a 1x1 pixel SVG element with an "onload" handler. The compromise is visually invisible, and scanners don't detect it, but the malicious code is still active. The
"onload" attribute hides the skimmer's entire payload, encoded in base64 via an atob() call and triggered via setTimeout. The experts explain that the attackers don't use external scripts or suspicious links that could alert monitoring systems. The malware is embedded entirely within the page's markup in a single string.
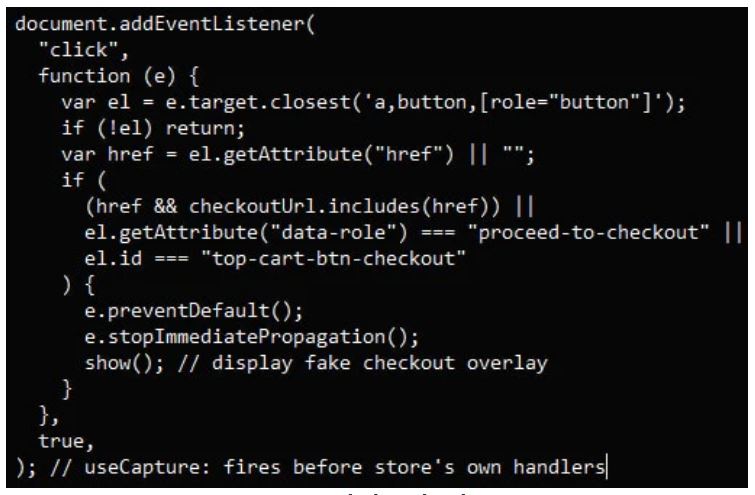
When a customer clicks the "Checkout" button in an infected store, the script intercepts the click and displays a fake "Secure Checkout" window over the page, complete with fields for entering the card number and billing address. This data is validated using the Luhn algorithm in real time and then sent to the attackers: the payload is first XOR-encoded, then base64-encoded, and transmitted to the hackers' server in JSON format.
Researchers identified six data exfiltration domains, all hosted by IncogNet LLC (AS40663) in the Netherlands. Each domain received data from 10-15 confirmed victims.
According to the researchers, the entry point was most likely the recent PolyShell RCE vulnerability , which became known in mid-March. The bug affects all stable installations of Magento Open Source and Adobe Commerce version 2 and allows for arbitrary code execution without authentication, as well as account takeover.
Sansec previously warned that more than half of all vulnerable stores were subject to PolyShell attacks (some of which were ultimately infected with skimmers for data exfiltration via WebRTC).
It's worth noting that Adobe developers have not yet released a patch for production versions of Magento. Currently, the fix is only available in the pre-release 2.4.9-alpha3+, and the company is not commenting on the vulnerability or its exploitation.
Until the official patch is released, experts recommend implementing all available security measures and, if possible, updating to the latest beta version of Magento.
