- 907
- 246
An international operation coordinated by Europol disrupted the operations of Tycoon2FA, one of the largest phishing-as-a-service (PhaaS) phishing platforms. During the operation, law enforcement officers seized 330 domains, including control panels and phishing pages. The technical component of the operation was led by Microsoft
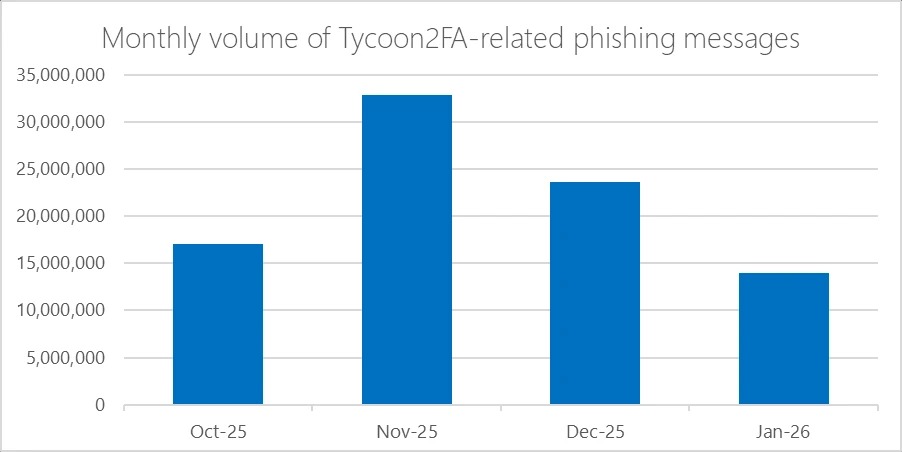
specialists with the support of a coalition of private partners. Law enforcement agencies from Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom were involved in the infrastructure seizure. The investigation began after Trend Micro analysts shared initial threat intelligence with Europol. Cloudflare, Coinbase, Intel471, Proofpoint, Shadowserver Foundation, SpyCloud, eSentire, Resecurity, and other organizations also provided assistance. Tycoon2FA (also known as Tycoon 2FA, believed to be operated by the Storm-1747 group) was operational since August 2023, allowing attackers to bypass multi-factor authentication (MFA) during account attacks. According to Microsoft, by mid-2025, the platform was generating tens of millions of phishing emails monthly, targeting over 500,000 organizations. Tycoon2FA accounted for 60% of all blocked phishing attacks. Nearly 100,000 organizations worldwide fell victim to the platform, including government agencies, schools, and healthcare organizations. Technically, Tycoon2FA was an AITM platform: a reverse proxy intercepted victims' credentials and session cookies in real time during attacks on Microsoft and Google users. This meant that the authorization process appeared normal to the victims, but the attackers were able to hijack an already authenticated session and bypass MFA. As Microsoft explained, the platform allowed attackers to impersonate login pages for popular services such as Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail. Captured session cookies and credentials remained valid even after password changes, until active sessions and tokens were manually revoked. MFA codes were relayed through Tycoon2FA proxy servers directly to the target authentication service. Subscriptions to the platform were sold through Telegram for $120 for 10 days of access. The low entry threshold allowed even low-skilled attackers to conduct large-scale phishing attacks.
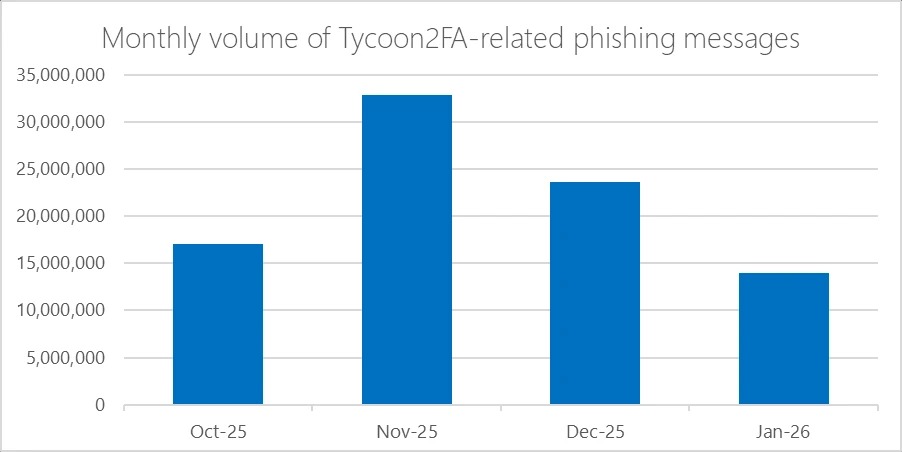
specialists with the support of a coalition of private partners. Law enforcement agencies from Latvia, Lithuania, Portugal, Poland, Spain, and the United Kingdom were involved in the infrastructure seizure. The investigation began after Trend Micro analysts shared initial threat intelligence with Europol. Cloudflare, Coinbase, Intel471, Proofpoint, Shadowserver Foundation, SpyCloud, eSentire, Resecurity, and other organizations also provided assistance. Tycoon2FA (also known as Tycoon 2FA, believed to be operated by the Storm-1747 group) was operational since August 2023, allowing attackers to bypass multi-factor authentication (MFA) during account attacks. According to Microsoft, by mid-2025, the platform was generating tens of millions of phishing emails monthly, targeting over 500,000 organizations. Tycoon2FA accounted for 60% of all blocked phishing attacks. Nearly 100,000 organizations worldwide fell victim to the platform, including government agencies, schools, and healthcare organizations. Technically, Tycoon2FA was an AITM platform: a reverse proxy intercepted victims' credentials and session cookies in real time during attacks on Microsoft and Google users. This meant that the authorization process appeared normal to the victims, but the attackers were able to hijack an already authenticated session and bypass MFA. As Microsoft explained, the platform allowed attackers to impersonate login pages for popular services such as Microsoft 365, OneDrive, Outlook, SharePoint, and Gmail. Captured session cookies and credentials remained valid even after password changes, until active sessions and tokens were manually revoked. MFA codes were relayed through Tycoon2FA proxy servers directly to the target authentication service. Subscriptions to the platform were sold through Telegram for $120 for 10 days of access. The low entry threshold allowed even low-skilled attackers to conduct large-scale phishing attacks.